CYBER SECURITY TRAINING
Prepare for the CompTIA Security+ Exam
Learn the latest skills to defend corporations and the country’s data from cyberattacks in our cyber security training program. Prepare yourself to play a pivotal role safeguarding major IT infrastructure in less than 8 months!
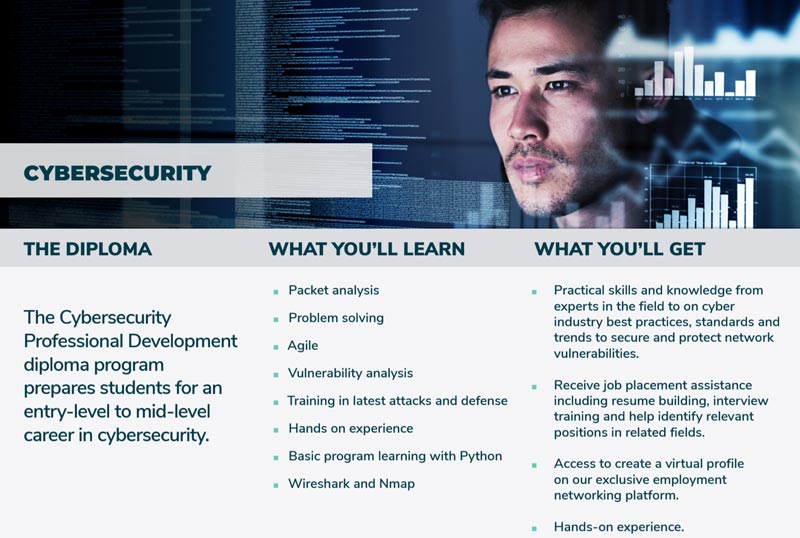
Cybersecurity Training Overview
Learn fundamental cybersecurity concepts to uncover organizations’ technological vulnerabilities. Fortify networks with cutting-edge hardware and software defense tools. Put your security training to work to take down cyber attacks.
Learn Cybersecurity Skills
Cybersecurity skills are in-demand across an array of industries. Training can help you learn them.
But, what skills can you expect to learn from our cybersecurity program?
Available Now in Our Partner Schools
Through our network of accredited partner schools, you will receive Woz U curriculum created by industry experts and employers to enhance your career development.
Why is WOZ Learning Different
Cybersecurity Courses
Data and property destruction; business disruption; proprietary data; intellectual property; and strategic information theft are all problems that is occurring in today’s society.
Get the skills to stop them with our comprehensive cybersecurity training curriculum.
Cyber Security Training Testimonials
Hear from past students how Woz U online cybersecurity courses has impacted their personal and professional development.
“When I started with Woz-U, I was working in an entirely different field of work, and had no prior cyber experience or knowledge coming in. The instructors, classes and labs took me through the need to know knowledge for today’s cyber roles. One instructor told me basically you learn half of Network+, all of Security+, and half of Pentest+. I have to say it was a pretty accurate representation, and after graduating from the program, I was able to do a little review and studying for Security+, and passed it on my first attempt. The program helped me make a significant career change, and one that I am excited for. The instructors I worked with were both very knowledgeable in the field and have a lot of great experience to share with students. Lastly, this online program is also one of the most cost effective at the time I had enrolled, and anyone looking to do a career change into cyber who doesn’t want to spend another 20-30 thousand at a traditional university setting, I strongly encourage you to check this program out. Thank you Woz-U.”
–Peter Soverns
Cyber Security Woz-U Grad
Other Topics You May Be Interested In
What Are the Branches of Cybersecurity?
Depending on the source, there are anywhere from three to six branches of cybersecurity. Initially, there was just cybersecurity without specialties. As the world of cybercrime went from hackers in a basement to organized groups [...]
How Does Cybersecurity Help Businesses?
You may be asking yourself how does cybersecurity help businesses? Isn't a firewall and anti-virus software enough? Businesses need cybersecurity professionals who have up-to-date knowledge of the best cyber programming languages and security measures to take. [...]
Best Programming Languages for Cyber Security
Since Cyber Security is all about keeping up with hackers, you'll want to make sure that you too are on the cutting edge of technology—especially in regards to IT infrastructure, networks, and software development.
The Cyber Security Skills Gap Affects Everyone
Research from the Center for Cyber Safety and Education predicts that the cyber security skills gap will increase to 1.8 million unfilled jobs by 2022, which represents a 20% increase over the forecast made in [...]